Wireguard VPN configuration in 5 minutes!
It's always more secure to connect with VPN when using RDP or SSH. Perhaps you want to access some services that are on a server from your laptop without exposing them to the public network.
You'll see how simple it is with Wireguard!
Before you proceed:
Configs for Windows and Linux are pretty much the same.
You can download Wireguard from here: wireguard.com/install.
Install it on both sides. In this article, we will use names Server and Station (for example your laptop).
I showed examples where the Server and Station run on the same OS, but they can be combined.
We will use the default 51820/udp port so make sure that it's opened on your server.
Windows
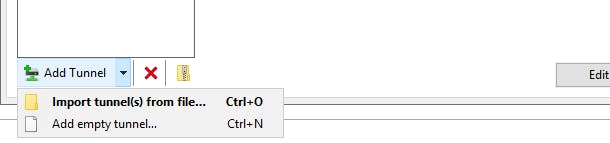
[Server] [Station] Open Wireguard and choose "Add empty tunnel..."
It'll automatically generate the Public and the Private key.
WARNING! Don't use the keys from this article!
[Server] Auto-generated keys example:
PublicKey: TwmGRV4TDmXrkHeNTJn2CXVi+lkOIyWcWDsLwi98A2Y=PrivateKey: kCDhb+rNp+mpRcuJ5KTn09eauqdhbrkb84VX91DWClE=
[Station] Auto-generated keys example:
PublicKey: aYV0p1OSm3apQqEUwd7UzUObsq7coA+u0ka2mNDpYHU=PrivateKey: 4Aj5+5rHJM0QL7dv9R85prVqEZuC6SCJvE31oGBdLGY=
[Server] Config:
[Interface] # the auto generated private key: PrivateKey = kCDhb+rNp+mpRcuJ5KTn09eauqdhbrkb84VX91DWClE= # the port that will be used for VPN tunnel: ListenPort = 51820 # the Server IP for VPN tunnel, you can leave it as it is: Address = 10.0.0.1/32 [Peer] # put here the public key from the Station: PublicKey = aYV0p1OSm3apQqEUwd7UzUObsq7coA+u0ka2mNDpYHU= # the Server IP for VPN tunnel, you can leave it as it is: AllowedIPs = 10.0.0.2/32**[Station] **Config:
[Interface] # the auto generated private key: PrivateKey = 4Aj5+5rHJM0QL7dv9R85prVqEZuC6SCJvE31oGBdLGY= # the Server IP for VPN tunnel, you can leave it as it is: Address = 10.0.0.2/32 [Peer] # put here the public key from the Server: PublicKey = TwmGRV4TDmXrkHeNTJn2CXVi+lkOIyWcWDsLwi98A2Y= # the Server IP for VPN tunnel, you can leave it as it is: AllowedIPs = 10.0.0.1/32 # replace the 1.2.3.4 with the public IP of the Server: Endpoint = 1.2.3.4:51820[Server] [Station] Set names, save and activate them on both sides!
[Station] Now you should be able to reach exposed server services using 10.0.0.1 IP from the Station!
Linux Debian 11
[Server] [Station] Open your favorite CLI and go to
/etc/wireguarddirectory.[Server] [Station] To generate keys run the following command:
wg genkey | tee privatekey | wg pubkey > publickey
WARNING! Don't use the keys from this article!
[Server] Auto-generated keys example:
PublicKey: TwmGRV4TDmXrkHeNTJn2CXVi+lkOIyWcWDsLwi98A2Y=PrivateKey: kCDhb+rNp+mpRcuJ5KTn09eauqdhbrkb84VX91DWClE=
[Station] Auto-generated keys example:
PublicKey: aYV0p1OSm3apQqEUwd7UzUObsq7coA+u0ka2mNDpYHU=PrivateKey: 4Aj5+5rHJM0QL7dv9R85prVqEZuC6SCJvE31oGBdLGY=
[Server] Create a
/etc/wireguard/wg0.conffile with contents:[Interface] # the auto generated private key: PrivateKey = kCDhb+rNp+mpRcuJ5KTn09eauqdhbrkb84VX91DWClE= # the port that will be used for VPN tunnel: ListenPort = 51820 # the Server IP for VPN tunnel, you can leave it as it is: Address = 10.0.0.1/32 [Peer] # put here the public key from the Station: PublicKey = aYV0p1OSm3apQqEUwd7UzUObsq7coA+u0ka2mNDpYHU= # the Server IP for VPN tunnel, you can leave it as it is: AllowedIPs = 10.0.0.2/32[Station] Create a
/etc/wireguard/wg0.conffile with contents:[Interface] # the auto generated private key: PrivateKey = 4Aj5+5rHJM0QL7dv9R85prVqEZuC6SCJvE31oGBdLGY= # the Server IP for VPN tunnel, you can leave it as it is: Address = 10.0.0.2/32 # enable ipv4 forwarding PreUp = sysctl -w net.ipv4.ip_forward=1 [Peer] # put here the public key from the Server: PublicKey = TwmGRV4TDmXrkHeNTJn2CXVi+lkOIyWcWDsLwi98A2Y= # the Server IP for VPN tunnel, you can leave it as it is: AllowedIPs = 10.0.0.1/32 # replace the 1.2.3.4 with the public IP of the Server: Endpoint = 1.2.3.4:51820[Server] [Station] After saving changes run the following command to start the tunnel:
wg-quick up /etc/wireguard/wg0.conf[Station] Now you should be able to reach exposed server services using 10.0.0.1 IP from the Station!
